Cyber Security Insights for Resilient Digital Defence
Cyber Security Insights for Resilient Digital Defence
Data Centre Security: Protecting Infrastructure from Physical and Cyber Threats
News
Feature - Reducing the impact of cyber attacks with rapid detection
By Eric Herzog, CMO at Infinidat.
There are constant headlines reporting cyber attacks on enterprises and preparing for the inevitability of cyber crime is absolutely critical. Yet despite such a widespread expectation of cyber attacks, there's a concerning lack of preparedness. Research conducted by the Ponemon Institute in 2023 suggests that only 35% of enterprises say they feel properly prepared to deal with a cyber security incident. And even among the ones that are prepared, there’s a general acceptance of vulnerabilities within their defences and reactions that they are not fully prepared for. Hackers will exploit this to the maximum.
Three major costs of a cyber attack
When a cyber attack does occur, and enterprise data becomes compromised, huge costs, operational disruption, and reputational damage are incurred. Let’s examine these impacts individually. The financial impact of data breaches is substantial and continues to rise. According to the Ponemon research, the global average cost of a data breach increased by 10% to $4.88 million, which is the highest ever recorded.
Cyber attacks, as we all know, also significantly disrupt business operations. According to Statista research, it took an average of 64 days to contain a breach in 2024 and in cases where stolen or compromised credentials were involved, this increases significantly. Such an extended period of disruption can severely impact a company's ability to function normally, potentially leading to lost productivity, lost revenue, and lost profits.
And let’s not overlook the reputational impact of data breaches, which leads to loss of business in the longer term. This is, perhaps, the most costly aspect of a cyber attack, because the intangible values of customer trust and loyalty are significantly affected. Depending on the industry, this cost can vary significantly, with the healthcare, financial services, technology and service sectors being the most expensive to recover from. In the UK, the Ponemon research cites the average cost of recovery within these industries was £5m.
What enterprises need to properly prepare for and counter these attack threats is powerful, easy-to-manage data protection and backup storage solutions, combined with guaranteed cyber storage resilience. This is because the speed at which a cyber attack occurs requires immediate and coordinated responses - from all levels of an organisation.
A need for ‘baked in’ cyber storage resilience
Using a software-defined storage architecture with integrated cyber storage resilience technology is one good way to minimise these impacts. When cyber storage resilience is embedded into enterprise storage, it allows for sub-second protection response and recovery times. This is critical because, when confronting a cyber attack, losing time can cost tremendous amounts of money. Ultra-fast response times will significantly reduce a cyber event's potential cost and recovery impact. For instance, a backup repository involving multiple petabytes of storage could be fully recoverable in just a few minutes.
Here's an actual, real-world use case example to illustrate this. To protect the client’s confidentiality, I will just call them ‘Fortune Global 500 company’. This actual customer needed to improve its restore times for their Oracle databases without impacting on service. They were able to achieve an average seven-times improvement to the backup time of their databases using Infinidat. They also achieved a 97% reduction in recovery time for full copies and a 95% reduction to full physical back up times. In addition, backup integrity was fully verified and, after verification, could be converted to an immutable copy to protect against cyber attacks.
The five cyber essentials
What core cyber storage resilience capabilities were essential for this enterprise to have in place? There are five:
• Logical air-gapped protection: Leveraging the ability to isolate data sets logically, fully, and completely, without requiring secondary environments.• Immutable snapshots: Completely hardened and unchangeable data set protection, helping ensure your business is following a proper set of best practices.• Fenced forensic network: Dedicated networking resources activated only to surface a copy of the data to be inspected, tested, or recovered from, within a fully isolated, tightly managed network environment.• Near-instantaneous recovery of any size backup repository.• Data centre-wide cyber security integration, where enterprise storage is seamlessly integrated with data centre-wide cyber security software applications.
AI powered scanning
To extend their cyber prevention further, advanced cyber detection capabilities can validate the integrity of immutable snapshots using powerful, AI-based scanning engines. Comprehensive machine learning technology can detect ransomware and malware attacks with up to 99.99% accuracy, enabling enterprises to quickly and easily identify a last known good copy for rapid, intelligent recovery. This provides complete reassurance that the data has not been compromised.
A new standard for cyber resilient storage
What enterprises need from their storage platform today are outstanding performance levels, guaranteed availability, cyber storage resilience, ease of use, and cost savings - at scale and for any backup/recovery data protection use case. By their very nature, backups are the last resort for protecting and recovering critical data. The storage location for this critical data should embody enterprise-calibre reliability and resilience. It should come with SLA-based guarantees for performance, 100% availability, and cyber storage recoverability. This sets the standard for enterprise storage and backup use cases, ensuring the utmost safety and recoverability for critical, backed-up data. Infinidat allows customers to choose the solution that best fits their use case or environment, with a consistent and easy-to-manage set of solutions to save them time and money.
Action is critical
Extensive research clearly indicates that preparing for cyber attacks is not just advisable, but critical for business survival in the digital age. The inevitability of cyber threats means companies must invest in comprehensive preparation strategies to mitigate their risks, protect their assets, and ensure rapid response capabilities. This proactive approach is essential for maintaining business continuity and safeguarding against potentially devastating financial and reputational damages.
To read more from Infinidat, click here.
Simon Rowley - 8 January 2025
Cyber Security Insights for Resilient Digital Defence
Hyperscale Data Centres: Scale, Speed & Strategy
News
Schneider Electric announces Galaxy VXL UPS
Schneider Electric has announced the launch of its new Galaxy VXL – a highly efficient, compact, modular, scalable, and redundant 500-1250 kW (400V) three-phase uninterruptible power supply (UPS), complete with enhanced cyber security, software, and safety features.
At just 1.2m² with a power density of up to 1042 kW/m², Galaxy VXL UPS sets a new benchmark in efficient, sustainable, and advanced UPS technologies. Available immediately in all 400V IEC regions worldwide, Galaxy VXL delivers the highest levels of power performance for AI, colocation, and hyperscale data centre environments, as well as large-scale critical infrastructure and electrical systems within commercial buildings and industrial facilities.
With its industry-first compact design, high-density power provision, and AI-load tolerant design, Galaxy VXL maximises uptime and availability for the most energy-intensive infrastructure systems – being capable of powering up to 1.25 MW in one frame, and up to 5 MW with four units running in parallel, while increasing both operational and energy efficiencies to help minimise customers’ total cost of ownership (TCO).
Through its patented operating technologies, Galaxy VXL delivers up to 99% in its high-efficiency eConversion mode, and up to 97.5% efficiency in double conversion mode, providing Class-1 power protection alongside leading levels of energy reduction, while lowering the UPSs’ carbon emissions by a factor of two.
With a 52% smaller footprint compared with the industry average, its scalable, modular design also enables N+1 levels of redundancy to increase the system’s level of availability by a factor of 10. Further, through its modular architecture, customers can reduce their capital expenditure (CapEx) by purchasing power modules as they need them, enjoying optimised energy efficiency, and adding more power modules as demands grow.
Galaxy VXL is also compatible with both Lithium-ion and VRLA batteries, and with its Live Swap function, allows for greater uptime, availability, and easier serviceability – offering highly resilient, flexible, and predictable runtimes for data centre, IT, and critical electrical loads. This is complemented by anywhere remote monitoring via Schneider Electric’s EcoStruxure IT software, and enhanced security and ethernet connections, which are certified to the latest IEC 62443-4-2 security standards, providing a completely secure and connected remote management experience.
“As dependency on large-scale infrastructure systems grows at an unprecedented rate, it’s crucial that customers can access the most sustainable, resilient, and efficient technologies to safeguard their critical systems, while minimising their energy and environmental impact,” says Tarunjeet Sarao, SVP Data Centre Systems, Schneider Electric. “Our new Galaxy VXL UPS combines a compact, innovative, and highly efficient design with enhanced safety features, providing world-leading power protection for a wide range of AI, data centre, and industrial applications. This ensures the high-density workloads of the future are supported by unparalleled levels of reliability.”
Key features and benefits
Schneider Electric’s Galaxy VXL UPS has been designed to offer record breaking power densities, and an AI-ready power architecture for the most energy-intensive workloads. For the first time, this new UPS provides customers 1.25mw scalable and modular solution with 125kw/3U power modules in 1.2m² footprint, while being capable of supporting up to 1.25 MW of critical load in one frame and up to 5 MW with four units in parallel in only 4.8m² space.
Key benefits include:
• Modular, scalable, high-power design: With a power density of 1042 kW per squared meter, customers can deploy a 1.25 MW modular UPS in a single frame, and add power modules incrementally via pay-as-you-grow flexibility.• Smaller footprint: Standing at 1.2m², Galaxy VXL has a 52% footprint improvement compared with industry average, with full front access and no rear clearance, offering better power and space utilisation.• Increased efficiency and sustainability: Galaxy VXL provides up to 99% efficiency in eConversion mode and up to 97.5% efficiency in double conversion mode. Its compact footprint means raw material reduction, less packaging, and includes SPoT (Smart Power Test) mode for UPS and Power Module testing, saving electricity.• Lower CapEx and OpEx: Improved operational and energy efficiencies provide a catalyst for lower electricity bills, and ease of service/maintenance equates to lower labour cost for a better TCO.• Reinforced, resilient design: Galaxy VXL utilises conformal-coated boards, 100kA short circuit rating and optional seismic kit for a robust mechanical design.• Enhanced cyber security and safety: Galaxy VXL is certified to the latest IEC 62443-4-2 security standards and includes Live Swap technology to allow power module replacements, with zero downtime.• Extended lifespan via EcoCare: With Galaxy VXL, Schneider Electric is introducing EcoCare membership, a next-generation services plan, providing premium on-site and remote access to technical experts, 24/7 remote monitoring powered by AI, condition-based maintenance to minimise on-site disruptions by up to 50%, and help extend the UPS’s lifespan.• Perfect for prefabricated data centres: With a smaller physical footprint, higher efficiency, and lower cost, Galaxy VXL provides a resilient backbone for the prefabricated data centres of the future.
Scaling-up to customer demands for AI systems
To meet customer demands for AI systems, Schneider Electric has increased manufacturing and production capacity at a host of its global factories, where its annual production capacity for Galaxy VXL UPS will exceed 9,000 units in 2025.
Additionally, Galaxy VXL UPS will be available at Schneider Electric’s Sant Boi, Barcelona factory, where it will be integrated to form the resilient backbone for Schneider Electric’s prefabricated, modular range of high-compute workload data centre solutions.
Schneider Electric’s Galaxy VXL UPS is available for order immediately.
For more from Schneider Electric, click here.
Simon Rowley - 5 December 2024
Cyber Security Insights for Resilient Digital Defence
Data Centre Security: Protecting Infrastructure from Physical and Cyber Threats
News
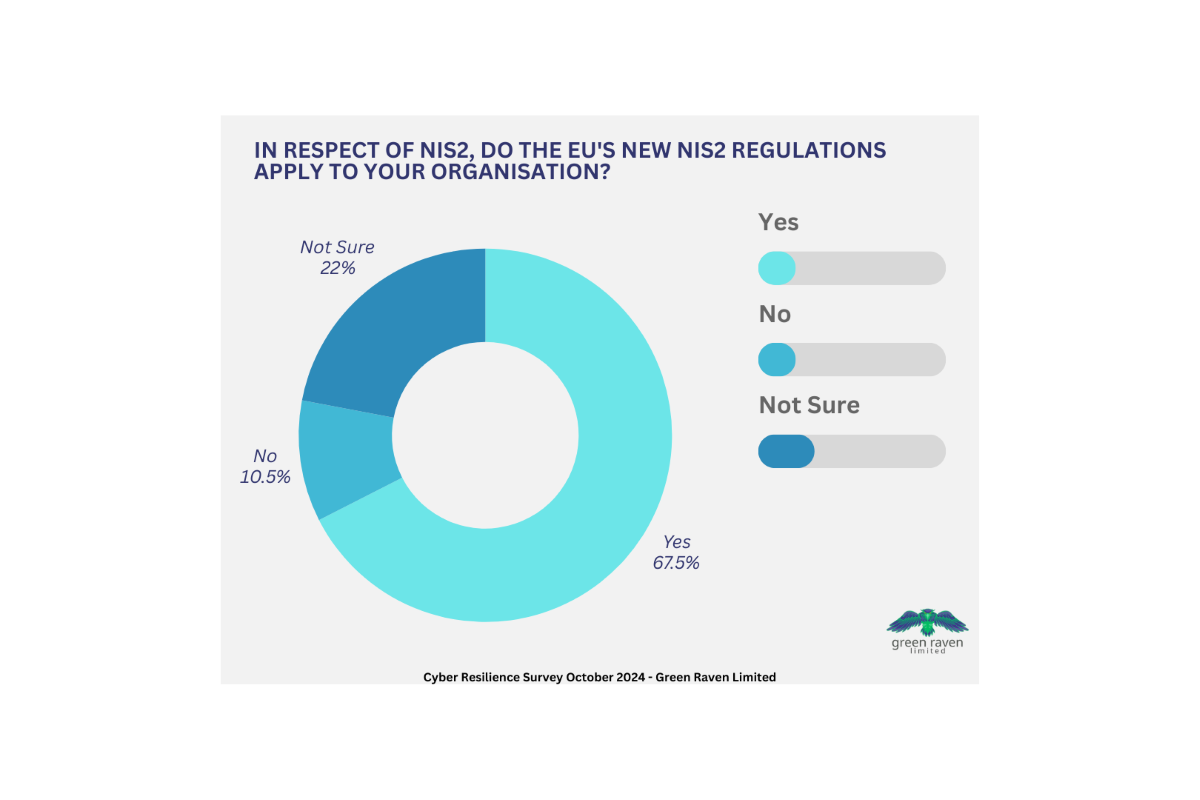
NIS2 still a mystery to cyber security bosses, research shows
Senior cyber security professionals at more than a fifth of the UK’s largest businesses are still “not sure” whether the EU’s NIS2 directive - which is the EU-wide legislation on cyber security - even applies to their organisation, new research by specialist cyber security consultancy, Green Raven, has revealed.
More than two-thirds of respondents at organisations with at least 1,000 employees said that NIS2 does apply to them, but almost 10% of these admitted that their organisation was not compliant as of the 17 October 2024 deadline – with a further 3% not sure.
The findings contradict previous research from June 2024, in which 97% of IT leaders at UK companies declared themselves confident that they would be, or already were, NIS2-compliant.
Morten Mjels, CEO of Green Raven, says, “NIS2 came into force in January 2023 – almost two years ago – so for senior cyber security professionals at the companies most likely to be impacted to not know if it even applies - wow. Saying, 'Yes, we’re compliant' may be acceptable; admitting that 'No, we’re not compliant but we’re working on it' may also be acceptable - assuming there may be a grace period when new regulations come into force.
“But, eventually, failure to be compliant is going to significantly impact the ability of these organisations to do business in Europe, or is going to attract a significant fine for doing business in Europe without being compliant. And saying, ‘We weren’t sure’ is unlikely to be much of a defence.”
The research also asked respondents for their reaction to the Cyber Security and Resilience Bill, trailed by the UK Government in July 2024’s King’s Speech. This new bill is expected to build upon the foundations laid by the EU’s Network and Information Systems (NIS) directive and is commonly seen as the UK’s response to the NIS2 directive.
Asked to react based on what they had heard or read about the new Act:
• 37% of respondents hope that the new Cyber Security and Resilience Bill won’t apply to their organisation, but almost 80% expect that it will.• 46% of respondents expect the bill to make unwanted demands of UK businesses, but over 82% expected the bill to make reasonable demands of UK businesses. A similar proportion agreed that the bill would make necessary demands of UK businesses.• Almost 88% of respondents agreed with the statement "The UK Cyber Security and Resilience Bill will improve the UK's overall cyber resilience”. Not a single respondent disagreed with the statement, despite the acknowledgement of the additional demands and overheads the new bill is likely to bring.
Morten comments, “While few details are known beyond the idea that it will be the UK’s equivalent of NIS2, the key takeaway from the research is that every cyber security professional asked clearly believes that there is more that organisations can, and will, be forced – via legislation – to do to improve their cyber security posture and resilience. As a cyber security professional in an organisation likely to be in scope, I wouldn’t be waiting for legislation.”
Conducted on its behalf by research specialist, Censuswide, Green Raven surveyed 200 respondents from among the UK’s 1,930 organisations with at least 1,000 employees. All respondents described their role as CISO/director/head/manager of (or in) their organisation's cyber security team.
The EU’s Network and Information Security Directive (NIS2) aims to improve the overall level of cyber security and standardise cyber resilience across the EU, by requiring operators of critical infrastructure and essential services to implement appropriate security measures and report any incidents to the relevant authorities. EU member states were required to transpose NIS2 into their national legislation by 17 October 2024. Although the UK has left the EU, NIS2 impacts UK organisations that fall under its scope and conduct business in the EU, either as a customer or as a supplier.
Green Raven is a specialist cyber security consultancy and reseller, applying decades of track record, experience and knowledge to bring together customers and cyber security solution providers. In particular, Green Raven is a white-label partner for Darkscope, which is predictive cyber threat intelligence for enterprises. Green Raven’s implementation of Darkscope’s unique, AI-powered portfolio of solutions spots cyber attacks that others can’t, and before they take place – so those responsible for cyber security can reinforce their cyber defences where they know they’re about to be needed.
Its Supply Chain Monitoring Service leverages advanced cyber intelligence techniques and cutting-edge technologies to provide comprehensive oversight of an entire supply chain network – a key objective of the NIS2 directive.
Simon Rowley - 2 December 2024
Cyber Security Insights for Resilient Digital Defence
Data
Data Centre Security: Protecting Infrastructure from Physical and Cyber Threats
Data Privacy Insights for Secure Digital Operations
News
Zimperium predicts data privacy emphasis in 2025
Nico Chiaraviglio, Chief Scientist and Krishna Vishnubhotla, VP Product Strategy & Threat Intelligence at Zimperium, is predicting data privacy emphasis, more evasive phishing attacks and a rise of sideloading for 2025:
Each year around this time, security leaders cast their predictions on how the industry will change in the new year. What new threats will arise? How will organisations shift their security priorities? Which cybercriminal tactics will increase and which will decrease? At Zimperium, our mission is to secure the mobile attack surface and to empower security teams to effectively manage and mitigate mobile threats. In light of the research data we’ve compiled across millions of mobile devices and mobile apps over this past year, we’ve sat down to think about what new mobile security trends and threats you can expect to see in 2025.
Prediction 1: Mobile Security Platforms Will Increasingly Address Data Privacy Concerns, Not Just Security
Mobile security plays a crucial role in addressing the needs of data privacy. However, we often see mobile security with the lens of threat defence and application security. But regulatory compliance is a key piece of the mobile security function and we predict that in 2025, we will see mobile security prioritising data privacy needs by implementing robust privacy-preserving technologies.
According to Zimperium’s 2024 Global Mobile Threat Report, 82% of organisations allow bringing your own device (BYOD) to work. And a recent survey from Tableau found that 63% of Internet users believe most companies aren’t transparent about how their data is used, with 48% having stopped shopping with a company because of privacy concerns. We will likely see more regulatory compliance baked into mobile security solutions, particularly around data handling and encryption standards. We are already seeing regulatory shifts in the financial sector, holding app developers accountable for any harm towards their end users due to external attacks.
Businesses are recognising that regulatory compliance features are a necessary piece of the mobile security stack, and they are seeking mobile security platforms that address both privacy and security needs.
Prediction 2: Social Engineering Attacks Will Keep Becoming More Sophisticated and Evasive, Traditional Phishing Defenses Fall Short
Social engineering has evolved considerably over the past year. In 2025, we predict that 'mishing' (mobile phishing) attacks will become so sophisticated and evasive that traditional tooling won’t be able to detect it. We will see the rise of AI-driven mobile malware capable of mimicking user behaviour, making it far harder to detect using traditional methods.
Verizon’s 2024 Mobile Security Index revealed that AI technologies are expected to intensify the mobile threat landscape, with 77% of respondents anticipating AI-assisted attacks, such as deep fakes and SMS phishing. A notable example was identified by Zimperium’s zLabs researchers on an Android-targeted SMS stealer campaign, which to date, researchers have found over 107,000 malware samples directly tied to the campaign.
In separate research, the zLabs team found a new variant of the FakeCall malware, revealing new traits present in this variant, including the ability to capture information displayed on a screen using the Android Accessibility Service. Similar to the above, we will continue to see the development of 'stealth mobile devices', or devices specifically designed to circumvent typical security measures..
This highlights a strategic evolution in mobile security – evasive cyberattacks are now the new normal as cybercriminals are becoming more sophisticated in their mobile phishing attacks.
Prediction 3: Non-Traditional Entry Points Will Escalate Enterprise Mobile Risk
Threat actors will increasingly exploit iOS shortcuts, configuration profiles, and sideloaded applications to breach enterprise security. Recent research unveiled the dangers of sideloading applications, the practice of installing mobile apps on a device that are not from the official app stores.
According to Zimperium’s 2024 Global Mobile Threat Report, financial services organisations saw 68% of its mobile threats attributed to sideloaded apps. In fact, zLabs researchers found that mobile users who engage in sideloading are 200% more likely to have malware running on their devices than those who do not. Riskware and trojans, applications that disguise themselves as legitimate apps, are the most common malware families found.
APAC outpaced all regions in sideloading risk with 43% of Android devices sideloading apps. To protect against the risk that comes from sideloaded apps, enterprises must effectively protect their mobile endpoints by adopting a multi-layered security strategy including mobile threat defence and mobile app vetting.
The prominence of trojans are highlighted in the report with the findings indicating that threats from sideloaded apps are primarily driven by riskware and trojans, which account for a staggering 80% of the malware observed. Additionally, Zimperium’s threat data shows that approximately one in four Android devices face this issue. While sideloading is much more prevalent on Android, the recent Digital Markets Act (DMA) is expected to increase its prevalence on iOS.
Cybercriminals are constantly scouring for ways to break in and compromise corporate networks. In 2025, they will ramp up efforts on targeting non-traditional entry points.
Prediction 4: Surge in Mobile-Specific Ransomware
Mobile-specific ransomware is a rapidly evolving threat that should be top of mind for every CISO. Zimperium’s Mobile Banking Heist Report provides early evidence of this shift: in 2023, 29 malware families targeted 1,800 mobile banking apps with several showing early-stage ransomware capabilities. These tactics are tailored for mobile, signalling a move beyond data theft toward extortion and ransomware schemes designed specifically for mobile platforms.
This trend is part of a larger increase in ransomware and extortion attacks across digital channels. According to the 2023 Verizon Data Breach Investigations Report (DBIR), ransomware or extortion was involved in nearly one-third of breaches, indicating a shift among traditional ransomware actors toward new methods, including mobile-focused extortion.
This shift is further confirmed by the Thales 2024 Data Threat Report, which notes that ransomware and malware remain some of the fastest-growing threats, with 41% of enterprises facing malware-related breaches this year alone. With ransomware attacks growing by 21% in 2024, attackers are increasingly exploiting mobile platforms due to their unique vulnerabilities and often weaker security postures.
For CISOs, this signals an urgent need to prioritise advanced app-level security, phishing defences, and proactive monitoring in mobile environments, as the connectivity and sensitive data handled by mobile devices make them prime targets for the next wave of ransomware.
Zimperium’s zLabs research team is on a mission to identify emerging threats to mobile security, exposing malware groups and their variants before they have a chance to wreak havoc on businesses' mobile ecosystem. Our team will remain on the pulse of these developments, keeping a close eye on how these predictions play out in the new year.
Simon Rowley - 29 November 2024
Cyber Security Insights for Resilient Digital Defence
Data Centre Security: Protecting Infrastructure from Physical and Cyber Threats
Data Centres
News
DigiCert unveils 2025 security predictions
DigiCert, a global provider of digital trust, has released its annual forecast of cyber security predictions for identity, technology, and digital trust that the company expects to shape the landscape in 2025 and beyond. These predictions provide a snapshot of the cyber security challenges and opportunities enterprises will encounter in the months ahead.
Prediction 1: Post-quantum cryptography takes off2025 marks a pivotal year when post-quantum cryptography (PQC) shifts from theoretical frameworks to real-world deployments. With impending announcements from the US National Security Agency (NSA) and growing compliance pressures, PQC adoption will surge, empowering industries to embrace quantum-resistant solutions.
Prediction 2: Chief Trust Officers take centre stageDigital trust becomes a boardroom priority, leading to a continued rise of Chief Trust Officers (CTrOs) who will oversee ethical AI, secure digital experiences, and compliance in an increasingly regulated environment.
Prediction 3: Automation and crypto-agility become a necessityWith industry shifts toward shorter SSL/TLS certificate lifespans, automation and crypto-agility will emerge as critical capabilities for organisations aiming to maintain secure operations amidst evolving standards.
Prediction 4: Content provenance goes mainstreamIn an era of deepfakes and digital misinformation, the Coalition for Content Provenance and Authenticity (C2PA) is set to redefine how we verify digital content. Expect to see C2PA’s Content Credential icon become commonplace on images and videos to enhance trust across media platforms.
Prediction 5: Organisations will demand resilience and zero outagesThe CrowdStrike outage this summer underscored the need for better testing of automated updates and stronger digital trust. As IoT adoption grows, concerns about the safety of over-the-air updates, particularly for self-driving cars, are prompting calls for greater transparency in security practices. The EU’s Cyber Resilience Act, effective in 2027, will drive stricter cybersecurity standards, fostering a more secure and trustworthy IoT ecosystem.
Prediction 6: AI-driven phishing attacks will surgeThe proliferation of AI will fuel an unprecedented surge in sophisticated phishing attacks, making them harder to detect. Attackers will leverage AI to craft highly personalised and convincing phishing campaigns, while automated tools will enable them to scale attacks at an alarming rate, targeting individuals and organisations with precision.
Prediction 7: New private PKI standards like ASC X9 will gain momentumASC X9 is poised to gain momentum as industries like finance and healthcare increasingly require customised security frameworks to meet stringent regulatory demands and unique operational needs. Unlike public PKI, ASC X9 offers greater flexibility by enabling tailored policies and trust models, addressing critical areas such as data integrity and authentication. This ability to foster secure, scalable, and interoperable frameworks will make ASC X9 a preferred standard for organisations prioritising trust and collaboration.
Prediction 8: Cryptography Bill of Materials (CBOM) gains tractionIn response to escalating cyber security threats, CBOMs will become a vital tool for ensuring digital trust by cataloguing cryptographic assets and dependencies, enabling better risk assessments.
Prediction 9: The era of manual certificate management wndsManual management of certificates, still common in nearly a quarter of enterprises, will phase out as automation becomes indispensable for handling shorter certificate lifespans and stricter security protocols.
Prediction 10: Organisations will continue to prioritise fewer vendorsDespite concerns about single-vendor risks and a peak of venture capital funding for AI start-ups, enterprises will continue to consolidate vendors to simplify management, improve integration, and enhance overall security practices.
“The relentless pace of innovation is not just reshaping our digital lives - it’s exposing new vulnerabilities faster than we can secure them, demanding a bold rethinking of how we approach cyber security,” says Jason Sabin, CTO at DigiCert. “The predictions for 2025 underscore the urgent need to stay ahead of these vulnerabilities by driving quantum readiness, enhancing transparency, and reinforcing trust as the bedrock of our rapidly changing digital ecosystem. DigiCert remains committed to shaping and securing future digital innovation to remain ahead of the vulnerability curve.”
For more from DigiCert, click here.
Simon Rowley - 25 November 2024
Artificial Intelligence in Data Centre Operations
Cyber Security Insights for Resilient Digital Defence
Data
Data Centre Operations: Optimising Infrastructure for Performance and Reliability
News
AI security and data availability to underpin 2025 tech trends
AI has continued to be transformative throughout 2024, with accelerating adoption by enterprises and a growing number of use cases. According to experts from data platform, Nasuni, the AI boom will continue in 2025, but will be defined by three key pillars:
1. 2025 will bring a new era of security maturity - The ability to protect and quickly recover data assets underpins every other business process in an AI-first world
2. Data readiness will be central to AI success - As we look toward 2025, data will no longer just support AI, it will shape and limit the scope of what AI can achieve
3. Enterprises will strive to find the real ROI in AI - 2025 will usher in a more measured approach to AI investment, as organisations will be increasingly focused on quantifiable ROI
Discussing these predictions, Russ Kennedy, Chief Evangelist at Nasuni, says, “In 2025, data will be more valuable than ever as enterprises leverage AI to power their operations. However, as data’s value grows, so does its appeal to increasingly sophisticated threat actors. This new reality will continue driving organisations to rethink their security frameworks, making data protection and rapid recovery the backbone of any AI strategy. Attackers are evolving, using AI to create more insidious methods, like embedding corrupted models and targeting AI frameworks directly, which makes rapid data recovery as vital as data protection itself.
“Businesses will need to deploy rigorous measures not only to prevent attacks, but to ensure that if the worst happens, they can quickly restore their AI-driven processes. 2025 will bring a new era of security maturity, one where the ability to protect and quickly recover data assets underpins every other business process in an AI-first world.”
Jim Liddle, Chief Innovation Officer Data Intelligence and AI at Nasuni, comments, “As we look toward 2025, data will no longer just support AI – it will shape and limit the scope of what AI can achieve. A robust data management strategy will be essential, especially as AI continues advancing into unstructured data. For years, companies have successfully leveraged structured data for insights, but unstructured data – such as documents, images, and embedded files – has remained largely untapped. The continued advancements in AI’s ability to process the different types of unstructured data that reside within an enterprise are exciting, but they also require organisations to know what data they have and how and where it’s being used.
“2025 will mark the era of ‘data readiness’ for AI. Companies that strategically curate and manage their data assets will see the most AI-driven value, while those lacking a clear data strategy may struggle to move beyond the basics. A data-ready strategy is the first step for any enterprise looking to maximise AI’s full potential in the coming years.”
Nick Burling, Senior Vice President, Product at Nasuni, adds, “2025 will usher in a more measured approach to AI investment, as organisations will be increasingly focused on quantifiable ROI. While AI can deliver immense value, its high operational costs and resource demands mean that companies need to be more selective with their AI projects. Many enterprises will find that running data-heavy applications, especially at scale, requires not just investment but careful cost management. Edge data management will be a critical component, helping businesses to optimise data flow and control expenses associated with AI.
“For organisations keen on balancing innovation with budgetary constraints, cost efficiency will drive AI adoption. Enterprises will focus on using AI strategically, ensuring that every AI initiative is justified by clear, measurable returns. In 2025, we’ll see businesses embrace AI not only for its transformative potential, but for how effectively it can deliver sustained, tangible value in an environment where budgets continue to be tightly scrutinised.”
For more from Nasuni, click here.
Simon Rowley - 18 November 2024
Cyber Security Insights for Resilient Digital Defence
Data Centre Security: Protecting Infrastructure from Physical and Cyber Threats
News
Integrity360 launches Managed dSOC Services
Integrity360, a pan-European cyber security specialist, today announced the launch of its Managed dSOC Services, an advanced security monitoring solution powered by Darktrace's AI-driven technology and Integrity360’s cyber security expertise.
The partnership allows Darktrace customers to gain access to an expert team dedicated to ensuring continuous, real-time monitoring, with around-the-clock expertise that internal teams may lack and to fully optimise and benefit from the capabilities of the platform.
The Managed dSOC Services are tailored to support businesses with proactive threat detection, rapid incident response, and continuous optimisation of their security investments, ensuring comprehensive protection against constantly evolving threats.
According to a recent report from Gartner, organisations that do not optimise and manage their cyber security solutions effectively may see a 30% increase in security incidents over the next three years. Integrity360’s Managed dSOC Service directly addresses this challenge by offering a fully managed service that takes the burden off internal teams, allowing businesses to focus on growth while ensuring optimal protection.
Eloina Pesce, Vice President of Channel, Darktrace, comments, “As organisations look to invest in AI-driven security tools like Darktrace, their internal teams may lack the time or skills to fully leverage them to their greatest benefit. Integrity360’s Managed dSOC fills a crucial gap for those organisations, helping them maximise their cyber security posture and reduce risk.
“Not only that, but Integrity360 experts build on the Darktrace ActiveAI Security Platform’s AI-driven detection and response with tailored services like proactive threat hunting and enhanced breach monitoring to provide an even greater level of protection.”
For Integrity360’s Darktrace customers, Integrity360’s Managed dSOC Services represent a critical enhancement to their cyber security investment. Darktrace’s platform, powered by advanced AI, offers unparalleled threat detection and real-time security insights. Augmenting this with Integrity360’s service capacity and expertise to fully manage the system will help organisations harness the platform’s full potential. Companies with a managed service like Managed dSOC will experience enhanced security optimisation, increasing further their return on investment from their Darktrace platform.
Integrity360’s Managed dSOC enables customers to fully capitalise on the benefits of their Darktrace investment, from 24/7 active monitoring to bespoke reporting and continuous AI model optimisation, ensuring clients not only detect threats in real time but also respond swiftly and strategically. With Integrity360’s specialised support, organisations can rest assured that their Darktrace environment is optimally configured, continually adapting to emerging cyber threats, and delivering maximum risk reduction.
“Through our partnership with Darktrace, we’re bringing an unmatched level of expertise and proactive support to our clients, allowing them to unlock the full potential of their cyber security investment,” says Brian Martin, Director of Product Management at Integrity360. “Nobody else can extract the same level of value out of the investment that we can, with this level of service and expertise underpinning it 24x7. Our Managed dSOC service suite brings this additional value within reach of all organisations irrespective of size, resources, or skill levels.”
The Managed dSOC service goes beyond traditional security operations by not only managing day-to-day monitoring, but also providing ongoing tuning and optimisation, incident support, and threat analysis to keep clients’ defences agile and aligned with current threats.
Integrity360’s Managed dSOC Services are available in three distinct tiers:• Managed dSOC: Core operational monitoring and breach detection, with daily reports for complete visibility and monthly health check• Managed dSOC+: Adds 24/7 active monitoring, high-value asset tagging, and periodic threat reviews for a more robust approach to security• Managed dSOC + MDR: Delivers advanced capabilities including threat response and proactive threat hunting
These flexible options allow businesses to select the level of support they require, from foundational monitoring to advanced threat detection and response, ensuring scalability as needs evolve.
Cyber security requires rigorous oversight and constant adaptation to new risks and Integrity360’s Managed dSOC Service addresses a prevalent universal challenge for most organisations: the cyber security skills and resource gap. Integrity360’s dedicated team of Darktrace experts ensures that every deployment is tailored to the client’s specific needs, refining configurations and implementing high-value security protocols to reduce exposure and enhance incident management.
As threats like ransomware, advanced phishing attacks, and supply chain compromises continue to surge, Integrity360’s Managed dSOC Services offer an essential service for companies seeking to strengthen their security posture while mitigating the complexity associated with managing AI-driven solutions. Managed dSOC Services represent a critical tool for businesses in high-risk sectors such as finance, healthcare, retail, government, and more, providing a comprehensive solution that combines advanced AI capabilities with expert oversight. By maximising the potential of Darktrace, organisations can minimise risk and confidently protect their critical assets.
Simon Rowley - 6 November 2024
Cyber Security Insights for Resilient Digital Defence
News
Aspire completes acquisition of CloudCoCo
Aspire Technology Solutions, a provider of managed IT, cyber security, and modern workplace technologies, has announced the acquisition of CloudCoCo, an experienced managed service provider headquartered in Leeds.
The acquisition marks a strategic advancement in Aspire’s plan to expand its UK presence and further strengthen its ability to deliver managed IT services, robust security solutions, and integrated modern workplace technology to clients across multiple industries, from SME to enterprise.
Building on Aspire’s successful acquisition of Cloud Cover IT in January 2024 - which expanded its footprint in Scotland and strengthened its service capabilities - CloudCoCo’s established relationships, skilled team, and expertise in managed IT, cloud, and unified communications will enable the Aspire Group to provide more tailored, responsive services that address the evolving needs of businesses across sectors. The acquisition will bring over £10 million in additional revenue and approximately 300 new customers to Aspire, setting the stage for future growth.
Chris Fraser, Aspire CEO and Founder, comments, “While CloudCoCo has undergone a period of structural transition, what truly stood out to us was its strong relationships with its high-quality customer base and the expertise within its team. These strengths align perfectly with our commitment to delivering technology like no other.
“This acquisition not only broadens our reach, but also enhances our ability to offer responsive, innovative solutions that meet the evolving needs of our clients. The CloudCoCo team will be an important part of Aspire’s next chapter, and together, we’re ready to make an even greater impact across key UK regions”.
Darren Weston, Group Operations Director at CloudCoCo, adds, “Joining Aspire represents an exciting new phase for CloudCoCo. We look forward to working closely with Chris and the team to expand our reach, deliver added value, and provide a wider range of innovative solutions. Aspire’s commitment to excellence aligns well with our own; it’s a powerful collaboration with a trusted UK technology provider that shares our values and goals.”
Aspire’s recent £1.7 million reinvestment in its established technology stack, as outlined in its FY24 accounts, reinforces the capabilities of its next-generation Security Operations Centre (SOC) and other critical infrastructure. Supported by LDC, a leading private equity firm known for backing high-growth UK businesses, this underscores Aspire’s dedication to driving innovation and maintaining the highest standards of service.
With an expanded presence across Gateshead, Glasgow, London, Stockton, and now Leeds, Aspire is seeking to set new benchmarks in managed IT, cyber security and modern workplace solutions for businesses throughout the UK.
For more from Aspire, click here.
Simon Rowley - 4 November 2024
Cyber Security Insights for Resilient Digital Defence
Data Centre Security: Protecting Infrastructure from Physical and Cyber Threats
Enterprise Network Infrastructure: Design, Performance & Security
News
Chief Telecom and RETN to enhance DDoS protection
Chief Telecom, a major telecommunications provider in Taiwan offering high-performance data centre services, network solutions, and cloud services, has partnered with RETN, a global network services provider, to leverage RETN’s newly launched DDoS mitigation platform.
The solution integrates RETN’s advanced DDoS mitigation technology with Chief Telecom’s strong IP Transit services customer portfolio, offering Chief Telecom’s customers protection against evolving cyber threats while maintaining high-quality, resilient internet connectivity. RETN’s platform provides automated threat detection and mitigation, leveraging machine learning to detect malicious traffic before it reaches the network, ensuring uninterrupted service even during large-scale cyberattacks.
In addition, the new platform benefits from RETN’s extensive global network, which connects Europe and Asia, making Taiwan a crucial point in this intercontinental link. The partnership ensures that Chief Telecom can offer businesses in Taiwan robust security features, including volumetric attack protection, application layer defence, and protocol attack mitigation, all supported by a 24/7 Security Operations Centre (SOC) and real-time alerts.
Tim Chiang, Vice President of Chief Telecom, says, “By partnering with RETN, we are empowering our customers in Taiwan with world-class DDoS protection and resilient network connectivity. This collaboration ensures that businesses can operate without fear of downtime, even in the face of the most sophisticated cyber threats.”
Chief Telecom's Taipei Internet Exchange (TPIX) is one of the largest in Asia, connecting businesses and internet service providers (ISPs) across the region. Chief Telecom plays a key role in ensuring Taiwan’s status as a digital hub, delivering robust connectivity and innovative services to businesses in Taiwan and beyond.
As Taiwan grows into a global technology hub with one of the highest internet penetration rates in Asia, businesses face an increasing threat of cyber attacks, especially Distributed Denial of Service (DDoS) attacks. Taiwan’s position as a key gateway for Asia-Pacific internet traffic also increases its exposure to cyber security risks. Chief Telecom thus sought a solution that could provide customers with enhanced DDoS protection, ensuring uninterrupted and secure network services, which are critical for Taiwan’s data-driven economy and high-tech industries.
For more from Chief Telecom, click here.
Simon Rowley - 29 October 2024
Cyber Security Insights for Resilient Digital Defence
Data Centre Security: Protecting Infrastructure from Physical and Cyber Threats
Events
News
Online event to focus on critical aspects of threat intelligence
ThreatQuotient, a threat intelligence platform innovator, has announced the launch of Cyber Rhino Threat Week, an online event offering key insights from industry leaders and ThreatQuotient executives.
Together, they will tackle the most pressing aspects of threat intelligence management. The virtual event will run from 9-13 December and will examine the latest best practices in threat intelligence and addressing the ever-evolving landscape of cyber threats.
Throughout the week, cyber security leaders and practitioners from all sectors are invited to attend five dedicated one-hour sessions with multiple registration time options to suit the three regions: the Americas, EMEA and APAC.
Each session will focus on different aspects of threat intelligence providing guests with actionable insights and a comprehensive understanding of how to enhance the effectiveness of organisational threat intelligence programmes and initiatives.
Commenting on the event, Gigi Schumm, Chief Revenue Officer at ThreatQuotient, says, “Cyber security teams increasingly depend on the strength of collective intelligence, not just to protect their own organisations but their industry and ecosystem of partners.
“By equipping ourselves with and sharing the latest threat intelligence and best practices, we can develop strategies to prevent attacks and build industry-wide defences. Cyber Rhino Threat Week exemplifies this effort by gathering top industry insights from key players within the threat intelligence market such as the Head of SOC for Paris 2024, the President and CEO at Cyber Threat Intelligence, the EMEA Executive Director at FS-ISAC and the Technical Director for the National Directorate of Custom Intelligence and Investigations.”
This inaugural event underscores ThreatQuotient's commitment to promoting intelligence sharing and collaboration across organisations in order to develop industry-wide responses to cyber threats. With Cyber Rhino Threat Week, ThreatQuotient offers participants a forward-thinking perspective on the future of collective intelligence in cyber security.
The sessions featured include special guests and four partners (Dataminr, Team Cymru, Google Cloud and Cybersixgill) who are co-sponsors of the event.
For further details and registration, click here.
For more from ThreatQuotient, click here.
Simon Rowley - 23 October 2024

Head office & Accounts:
Suite 14, 6-8 Revenge Road, Lordswood
Kent ME5 8UD
T: +44 (0)1634 673163
F: +44 (0)1634 673173